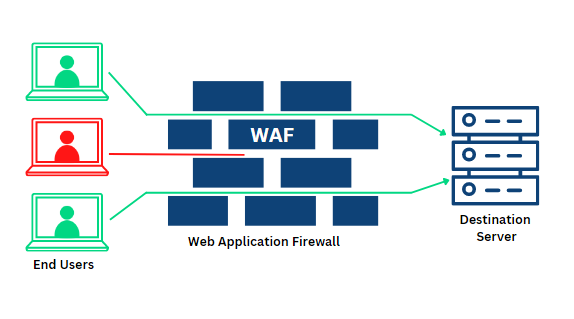
Web Application Firewalls are designed to protect web applications by blocking malicious and Spyware/Malware attacks.
A WAF inspects all requests that come into your web application in order to determine whether they are legitimate or if they are part of an attack.
All requests that are not identified as safe are sent to a security monitor to decide whether the request is harmless or a malicious attempt to access your data or components of your website.
If a request is determined to be suspicious, then the WAF will block it from entering your web application. This way, you can protect your data and keep your website safe from attack.
What is the difference between blocklist and allowlist WAFs?
Blocklist and allowlist WAFs are two security measures that you can use in your web application firewall (WAF). They are both used to block or allow traffic through a firewall based on the source IP address, destination IP address, or specific ports.
The key difference between blocklist and allowlist WAFs is that blocklist WAFs primarily use rules to reject traffic from untrusted sources, whereas allowlist WAFs primarily use rules to allow traffic from trusted sources. Allowlist WAFs can also be used to allow traffic from specific sources if the connection meets certain conditions.
You can think of blocklist WAFs as a way to protect your web application against attacks that originate from untrusted locations. By rejecting all network traffic from suspicious locations, you can ensure that attackers cannot reach your web applications.
On the other hand, allowlist WAFs are typically more relaxed than blocklist WAFs. They can still block traffic from untrusted sources, but they will also allow traffic from trusted sources if it meets certain conditions. This allows you to mitigate risks while still allowing legitimate users access to your web applications.
What are network-based, host-based, and cloud-based WAFs?
When it comes to web application firewalls, there are three different types of WAFs that networks can deploy: network-based, host-based, and cloud-based.
Network-based WAFs are typically implemented on the firewall perimeter and rely on the network to identify and then block traffic to and from ports on the firewall. This type of WAF is useful for mitigating attacks that originate from outside the firewall but can be problematic in two ways: first, it relies on the network infrastructure to function correctly, which can be disrupted by a outage; second, because application connections flow through switches and routers between the firewall and target servers, it is difficult to precisely block traffic using this type of WAF.
Host-based WAFs use an existing server running a host- Based intrusion detection system (HIDS) as the foundation for detecting malicious packets and then blocking them with rule sets based on signatures found within the HIDS. This type of WAF is more accurate than network-based WAFs at blocking most attacks but can be less reliable when attacking packets coming from outside the organization’s intranet boundaries or targeting known malicious applications.
Cloud-based WAFs are implemented as an independent service that resides in the cloud. The service uses machine learning algorithms to learn about malformed packets as they come inbound and then automatically blocks them using a set of predefined rules.
Despite their different approaches, all three types of WAFs have one common goal: protecting your web applications against malicious traffic. Network-based WAFs are particularly useful for mitigating Attacks that originate from outside the firewall perimeter while host-based or cloud-based WAFs provide additional accuracy and reliability when attacking packets coming from within or targeting known malicious applications.
Wrap up
If you need more information on Web Application Firewall (WAF), just reach out and my team will get back to you ASAP.


